Turn Coding Agents Into CI Gates
Skills are how you shape what an agent does during normal work. But sometimes you want a harder guarantee: something that runs on every PR, makes a pass/fail decision, and blocks merging until the condition is met. Blocks automations do exactly that. You configure the agent, write a prompt, pick a trigger, and flip one toggle to surface the result as a GitHub check.
Here is a concrete example. We wanted to enforce REST endpoint naming conventions on every PR to our orchestration service. The whole setup took a few minutes.
Configuring the automation
In the Blocks dashboard, we created an automation with OpenCode as the agent. The prompt is one line: use the endpoint naming skill to check whether the PR follows our naming guidelines. Trigger is set to GitHub Pull Request, scoped to BlocksOrg/orchestration-svc. Then one toggle: Display as CI check.
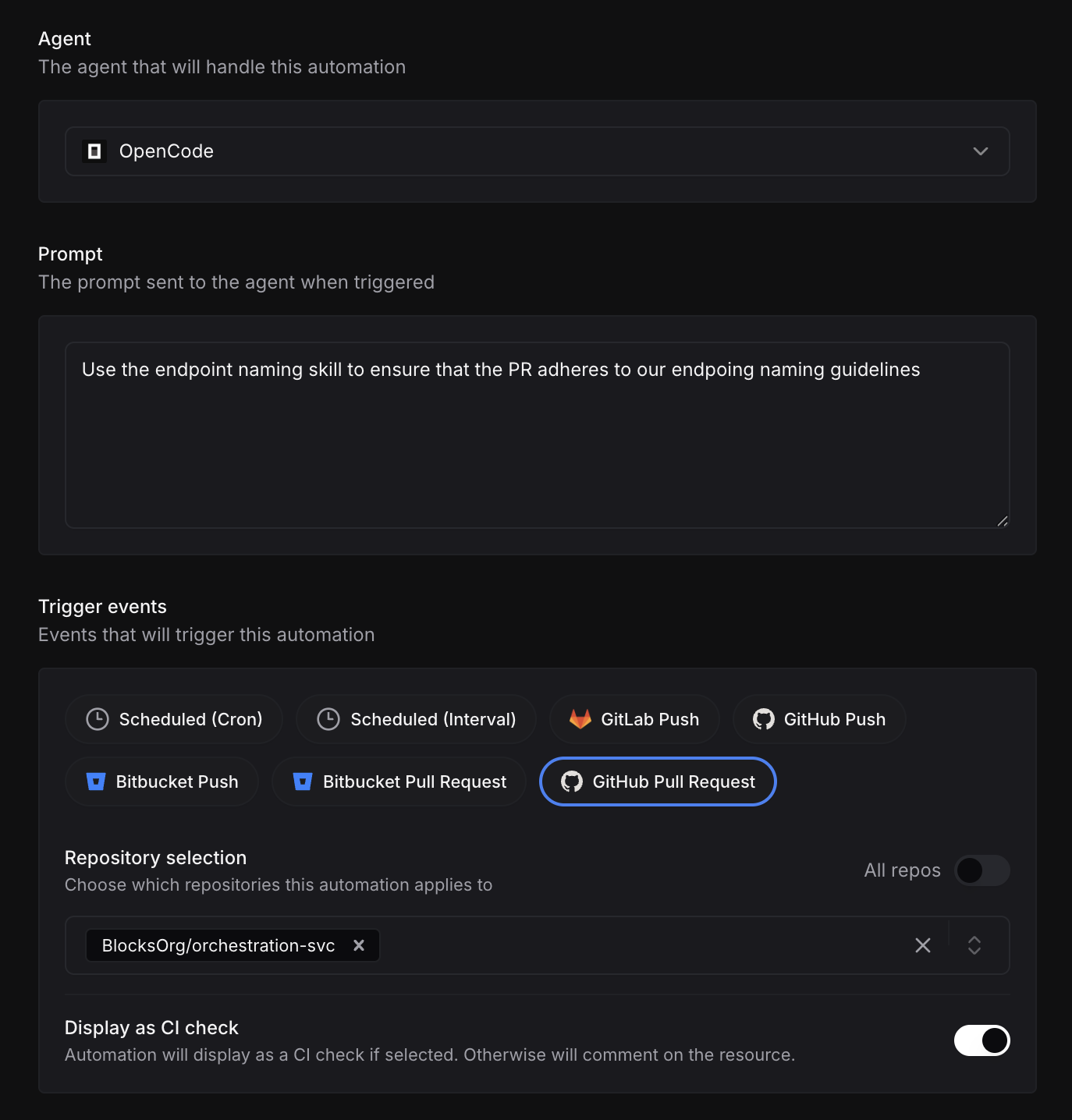
That toggle is the key distinction. Without it, the automation posts a comment. With it, the agent's verdict becomes a GitHub check status: pass or fail. To make it blocking, you mark the check as required in your repository's branch protection rules — the same way you would for any other CI check.
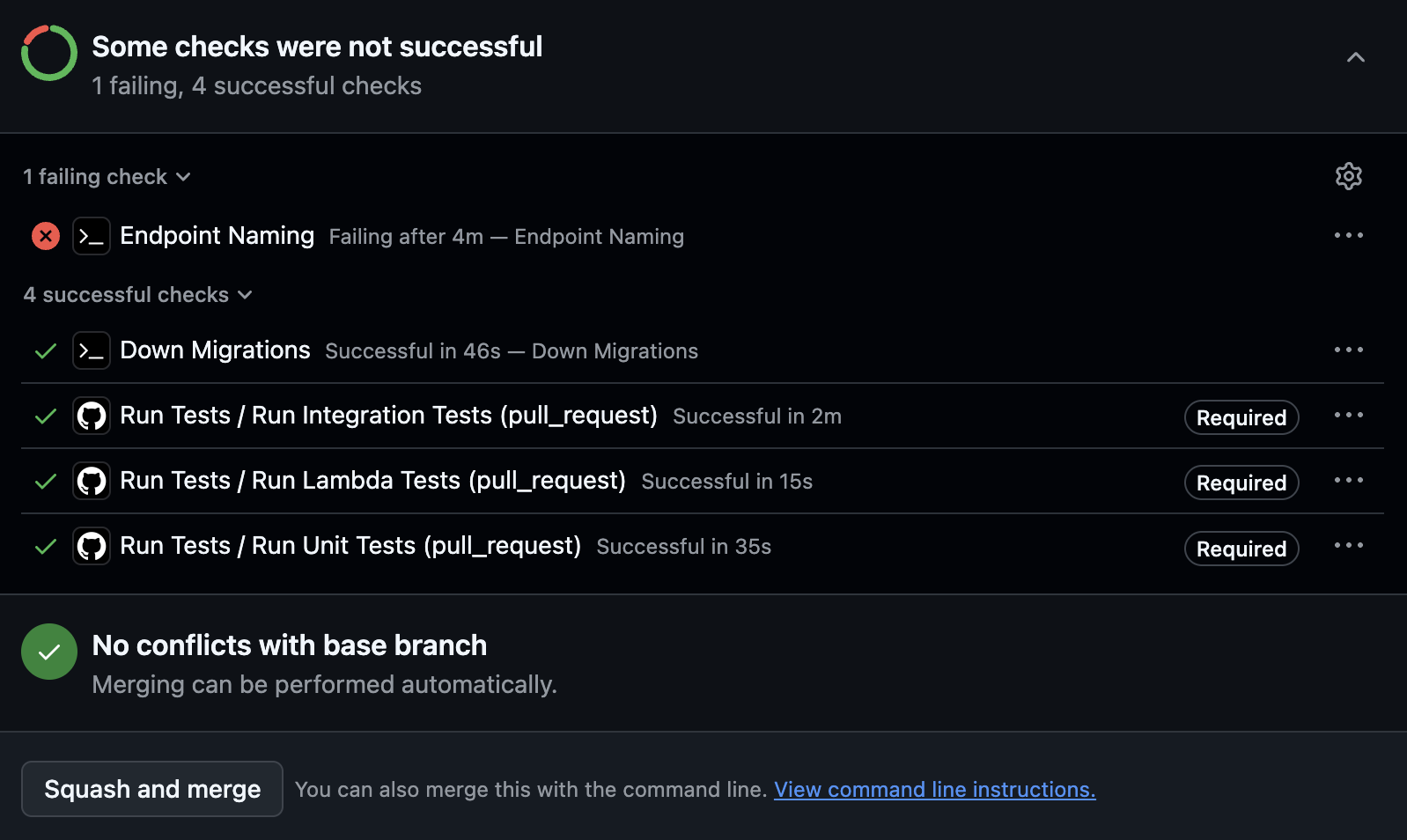
What it looks like in GitHub
Once the automation is live, it runs automatically on every PR. The check appears alongside your unit tests and integration tests. Mark it as required in your branch protection settings and a failing check prevents merging, the same as any other required check.
The agent gives specific, actionable output
Clicking into the failed check shows exactly what the agent found. In this case: four routes using snake_case path segments where kebab-case is the standard, and a redundant prefix on the history routes. The agent shows the current path and the corrected path side by side, and notes that the integration test BASE_URL will need to match.
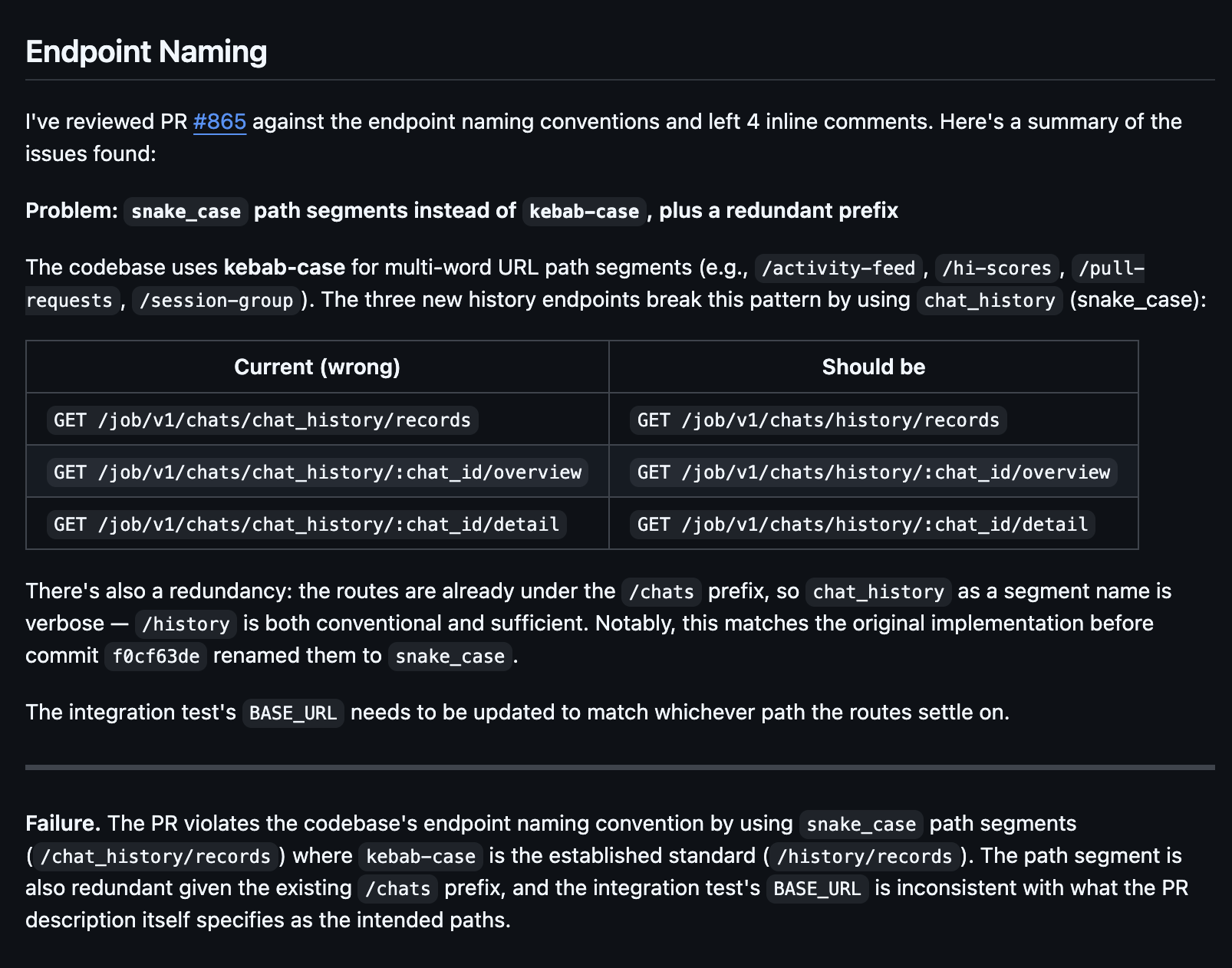
The developer knows exactly what to fix. No ambiguity, no back-and-forth in review comments.
Skills plus automations
Skills shape agent behavior during development. Automations enforce standards at merge time. The two layers complement each other: skills reduce the number of issues that reach a PR, and automations catch what gets through. Neither replaces the other. Together they give you consistent output without relying on code review to catch everything.
The same pattern applies to anything you want to enforce consistently: security checks, documentation requirements, migration conventions. If you can write a prompt for it, you can make it a CI gate.